TikTok vulnerability left users' personal data at risk of being hacked
A flaw was identified in the popular video-sharing app TikTok that would have let hackers scrape personal information from users’ accounts, according security researchers at Check Point.
Such details included phone numbers, nicknames, profile and avatar pictures, unique user IDs, as well as certain profile settings.
The vulnerability, found in TikTok’s ‘Find Friends’ feature, have have given bad actors enough information to connect between profile details and phone numbers.
With such information, attackers could have built a database of users and their related phone numbers to conduct malicious activity.
The issue would have only impacted those who have accounts linked to phone numbers or logged in with a phone number, according to the security researches.
However, Check Point says no evidence was found that the vulnerability was ever exploited and the flaw has reportedly been patched by TikTok.
Scroll down for video

A flaw was identified in the popular video-sharing app TikTok that would have let hackers scrape personal information from users’ accounts. Such details included phone numbers, nicknames, profile and avatar pictures, unique user IDs, as well as certain profile settings
Check Point spokesperson Ekram Ahmed said in a statement: ‘An attacker with that degree of sensitive information could perform a range of malicious activities, such as spear phishing or other criminal actions.’
‘Our message to TikTok users is to share the bare minimum when it comes to your personal data.’
Check Point researches took advantage of TikTok’s bug bounty program that launched earlier this year, which invites experts, coders and other computer enthusiasts to uncover any vulnerabilities that may be lurking in the app.
The cybersecurity firm found an issue in the ‘Friends Finder’ feature, which exposed personal information of certain users.

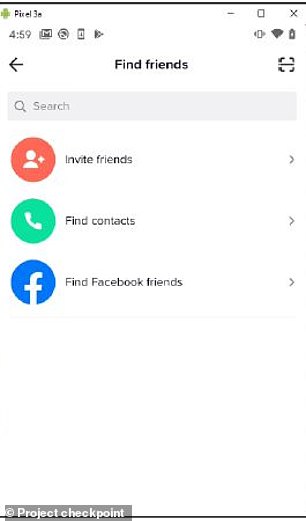
The vulnerability, found in TikTok’s ‘Find Friends’ feature, have have given bad actors enough information to connect between profile details and phone numbers.c
The TikTok app creates a user token and session cookie that are linked to a unique device ID for each user’s phone.
However, Check Point found session tokens were valid for up to 60 days, which allowed them to be used in virtual devices.
‘As our main purpose was to examine the privacy of TikTok, we focused on all actions related to users’ data,’ Eran Vakin and Alon Boxin, who conducted the research, shared in a statement.
‘The mobile application was found to enable contacts syncing, meaning that a user can sync his contacts to easily find people he knows on TikTok.
‘In simple words, it means that it is possible to connect between profile details and phone numbers.’
The team found they were able to bypass TikTok’s HTTP message signing with simple hacking tools, which allowed them to manipulate the function to collect contacts and re-sign the request.
And because the process was done using a virtual device, it could be setup to do so automatically.
A TikTok spokesperson said in a statement: ‘The security and privacy of the TikTok community is our highest priority, and we appreciate the work of trusted partners like Check Point in identifying potential issues so that we can resolve them before they affect users.’
‘We continue to strengthen our defenses, both by constantly upgrading our internal capabilities such as investing in automation defenses, and also by working with third parties.’
This is the second flaw Check Point has found in TikTok this year.
On January 8, the firm shared a set of vulnerabilities that could have allowed a threat actor to access personal information saved in a users’ accounts, manipulate users’ account details, or take actions on behalf of a user without their consent.